Documentation and FAQ
New to KeePassXC?
- Our Getting Started Guide will get you up and running quickly.
- Looking for more comprehensive documentation? Our User Guide is there to help.
- Need help troubleshooting the browser integration? Check the Setup Browser Integration section.
- Build instructions and other technical guides can be found in the GitHub Wiki.
- Looking for an audit of KeePassXC? Read the FAQ entry or Download the Audit Report.
Looking for ways to contribute?
You can contribute to the project by reporting bugs, proposing new features, writing code, translating, and / or donating.Frequently Asked Questions
General
-
Why KeePassXC instead of KeePassX?
KeePassX is no longer developed - as announced on the KeePassX website on 2021-12-09. Our decision to fork KeePassX was made some years prior, due to a sharp decline in code frequency at the time, combined with our wish to provide you with everything you love about KeePassX plus many new features and bugfixes.
-
Why KeePassXC instead of KeePass?
KeePass is a very proven and feature-rich password manager and there is nothing fundamentally wrong with it. However, it is written in C# and therefore requires Microsoft's .NET platform. On systems other than Windows, you can run KeePass using the Mono runtime libraries, but you won't get the native look and feel which you are used to.
KeePassXC, on the other hand, is developed in C++ and runs natively on Linux, macOS and Windows giving you the best-possible platform integration.
-
Which password database formats are compatible with KeePassXC?
KeePassXC currently uses the KeePass 2.x (.kdbx) password database formats KDBX 3.1 and KDBX 4 as its native file formats. KDBX 2 files can be opened, but will be upgraded to a newer format. KeePass 1.x (.kdb) databases can be imported into a .kdbx file, but saving a .kdbx file as .kdb would be lossy, and saving to .kdb is not supported by KeePassXC.
-
Why is there no cloud synchronization feature built into KeePassXC?
Cloud synchronization with Dropbox, Google Drive, OneDrive, ownCloud, Nextcloud etc. can be easily accomplished by simply storing your KeePassXC database inside your shared cloud folder and letting your synchronization service of choice do the rest. We prefer this approach, because it is simple, not tied to a specific cloud provider and keeps the complexity of our code low.
-
Does KeePassXC support (KeePass2) plugins?
No, KeePassXC does not support plugins at the moment and probably never will. KeePassXC already provides many of the features that need third-party plugins in KeePass2, so for most things you don't even need plugins, nor should you ever want them. Plugins are inherently dangerous. Many KeePass2 plugins are barely maintained (if at all), some have known vulnerabilities that have never been (and probably never will be) fixed, and none of them are as thoroughly tested and reviewed as we test and review code that goes into our main application. We find that encouraging users to install untested (and often quickly-abandoned) third-party plugins is inherently incompatible with the security demands of a password manager.
If you really need external functionality not available in KeePassXC, you can look for "plugins" that use the KeePassXC-Browser API, which is a much more secure way of sharing passwords with third-party applications than loading those applications as plugins directly into KeePassXC.
-
How can I add additional word lists to the passphrase generator?
You can add additional word lists to the passphrase generator by copying the word list file to the
share/wordlistsfolder inside your KeePassXC installation directory and then restarting KeePassXC.On Linux, the default install location is
/usr/share/keepassxc, on macOS it is/Applications/KeePassXC.app/Contents/Resourcesand on WindowsC:\Program Files\KeePassXC(orC:\Program Files (x86)\KeePassXCfor 32-bit).
Security
-
How can I migrate my database to KDBX 4?
In the Database application menu, select Database security.... Select the Encryption Settings tab and choose KDBX 4.0 (recommended). Press OK and save the database.
-
KeePassXC allows me to store my TOTP secrets.
Doesn't this undermine any advantage of two-factor authentication?
Yes. But only if you store them in the same database as your password. We believe that storing both together can still be more secure than not using 2FA at all, but to maximize the security gain from using 2FA, you should always store TOTP secrets in a separate database, secured with a different password, possibly even on a different computer.
-
Why would I use a password manager? Isn't it totally insecure to use
one password for everything?
Password reuse and simple, easy-to-guess passwords are the biggest problems when using online services. If one service gets compromised (either by guessing your password or by exploiting a security vulnerability in the service's infrastructure), an attacker may gain access to all of your other accounts.
But using different passwords for all websites is difficult without a way of storing them somewhere safe. Especially with arbitrary password rules for various services, it becomes increasingly hard to use both strong and diverse passwords. KeePassXC stores your passwords for you in an encrypted database file, so you only need to remember one master password. Of course, the security of all your services depends on the strength of your master password now, but with a sufficiently strong password, the password database should be infeasible to crack.
The database is encrypted with either the industry-standard AES256 or the Twofish block cipher and the master password is strengthened by a configurable number of key transformations to harden it against brute force attacks. Additionally, you can use a key file filled with an arbitrary number of random bytes or a YubiKey to further enhance your master key.
-
Has KeePassXC ever had an external security audit?
Yes, an audit was conducted by Zaur Molotnikov, an independent security consultant, and completed on January 19, 2023. This audit was conducted free of charge to the KeePassXC Team and the findings and writeup were reviewed for correctness. Download the Audit Report.
Keep in mind that:
- An audit is not 100% proof that software is safe and secure. Some flaws can be overlooked even by the best auditors.
- An audit is valid only for a “snapshot” of the code. If new code is added, new vulnerabilities can be introduced.
- Audits are expensive and time consuming, you can consult with OSTIF or OTF for funding additional KeePassXC audits.
-
I see that KeePassXC requires network access. What for?
KeePassXC needs network access for downloading website icons (favicons) for password entries. This feature is optional and opt-in. KeePassXC will never access any network resource without your explicit prior consent. If you don't use this feature, you may also compile KeePassXC without any networking code (see next question).
-
Can I get a KeePassXC version without any networking code?
Yes, you can compile KeePassXC without any networking code. Simply configure CMake with
-DWITH_XC_NETWORKING=OFF(see Building KeePassXC).
AppImage and Snap package
-
How do I execute an AppImage?
The AppImage is a self-contained executable archive, comparable to an Android APK or macOS DMG. To execute it, simply give the downloaded
*.AppImagefile execution permissions:1chmod +x ./KeePassXC-*.AppImageAfter that you can execute it either from the terminal or by double clicking it just like any other program.
-
What systems can I use the AppImage or Snap package on?
The AppImage should run out of the box on almost any moderately modern Linux distribution. The Snap is supported on all systems, which have
snapdinstalled. This is primarily Ubuntu, but also Debian, Fedora, OpenSUSE, Arch Linux and many more. For a full list and more information visit snapcraft.io. Note that not all systems that can run Snaps also support confinement via AppArmor. -
How do I use the KeePassXC CLI tool with the AppImage?
Starting with version 2.2.2, you can run the KeePassXC CLI tool from the AppImage by executing it with the
cliargument:1./KeePassXC-*.AppImage cli -
Why doesn't my theme work?
Since Snaps and AppImages are self-contained and mostly isolated from your system, they cannot know what theme you are currently running. This is a known issue with both Snaps and AppImages.
-
How do I get my YubiKey to work with the Snap?
Due to a Snap's isolation and security settings, you must manually enable the
raw-usbinterface in order to use your YubiKey. Issue the following command from a terminal to enable this interface:1sudo snap connect "keepassxc:raw-usb" "core:raw-usb" -
Why can't I see anything outside my home directory?
Due to Snap's isolation and security settings, you cannot access any files outside your home directory. Furthermore, you cannot access any hidden files within your home directory. The only exception is mounted USB drives, but you must type in
/media/into the file open dialog to see them.If you still cannot access the
/media/directory then you may need to enable this permission in the Ubuntu store. Open the Ubuntu store, choose the KeePassXC app, and click permissions.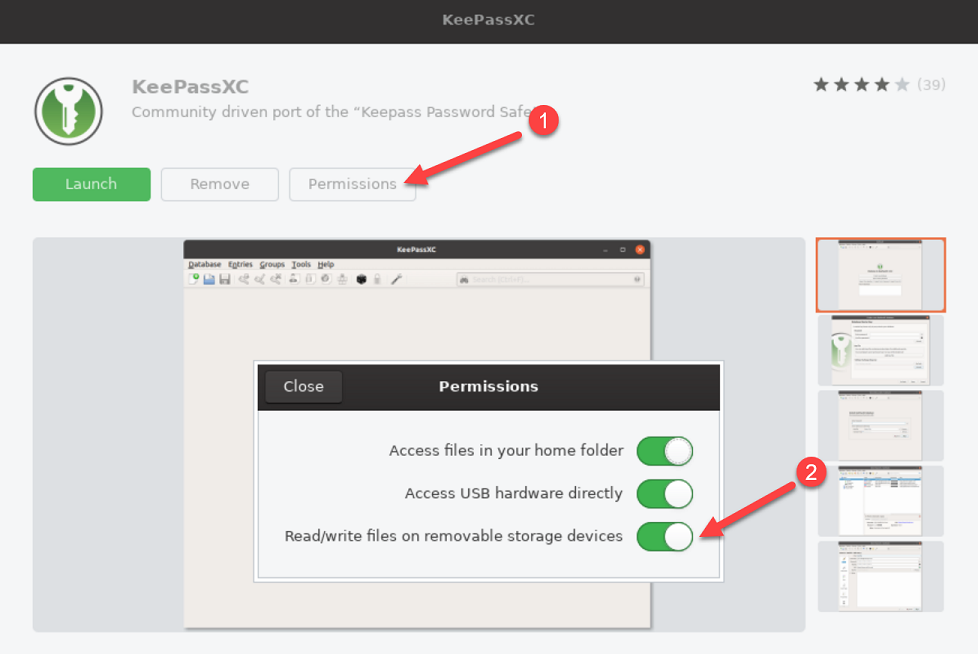
Snap Permission Settings
Key Files
-
What is a key file and how can I get one?
A key file is a file containing random bytes that can be added to your master key for additional security. Think of it as a really complicated and long password that is read from a file, so you don't have to remember or type it into your master password field. You can basically use any file you want as a key file, but it is of utmost importance that a) the file never changes and b) it actually contains unpredictable data. If the file changes, it is as if you forgot your password and you will lose access to your database.
On the other hand, if the data is not random enough, then it's a really bad password. So, for instance, a static and never-changing holiday picture is okay, your personal notes file is not. Generally, we recommend you let KeePassXC generate a dedicated key file for you. Go to Database -> Database Settings -> Security. There you click on Add Key File and then on Generate. Select the location where to save the key file, make sure the path to the new file is inserted into the Key File field, and save your database. Don't forget to keep a backup of the key file in a safe place!
-
How secure is a key file and how can I sync it to other devices?
A key file is only as secure as you keep it. It is basically a password that you've written down. As a general rule, you should never use a key file without an actual password, because it is harder to keep your key file secret than a memorized password that only you know. However, a key file can be very strong additional protection if kept separately from the database file, such as on an external thumb drive. If you sync your database via a cloud provider (Dropbox, Google Drive, Nextcloud, …), you should only sync the KDBX file and distribute the key file to your computers by different means, such as said thumb drive.
But whatever you do, keep a backup in a safe location! If you lose your key file, you lose your database. Keep in mind that USB thumb drives are notoriously unreliable, break easily, or get lost. If you can afford it, we recommend you use a hardware token such as a YubiKey or OnlyKey instead of a key file (see next section). Such a key adds an even greater amount of security, but with fewer potential pitfalls.
YubiKey / OnlyKey
-
Does KeePassXC support two-factor authentication (2FA) with YubiKeys or OnlyKeys?
Yes and no. No, because technically speaking, KeePassXC is not a service and therefore does not use "authentication". Instead, you are "decrypting" your database, which is different from "authentication". Nonetheless, you can improve the security of your database by use of a YubiKey in a slightly different way. KeePassXC generates a challenge and uses the YubiKey's response to this challenge to enhance the encryption key of your database.
So in a sense, it makes your password stronger, but technically it doesn't qualify as a separate second factor, since this is not an authentication scheme and also because the expected response doesn't change every time you try to decrypt your database. It does, however, change every time you save your database. Be aware, however, that the previous version of your database can still be decrypted with the old challenge/response (but no other version prior to that and no future version either).
-
How do I configure my YubiKey / OnlyKey for use with KeePassXC?
To use a YubiKey for securing your KeePassXC database, you have to configure one of your slots for HMAC-SHA1 Challenge-Response mode (see this video). Instructions on how to use your OnlyKey are found here. Once your hardware key is set up, open your database in KeePassXC, go to Database -> Database Security, click on Add additional protection, then Add Challenge Response. Once your key/slot is recognized, press ok and then save your database.
Important: Always make a copy of the secret that is programmed into your hardware key while you configure it and store in a secure physical location. If you lose or brick the key you will permanently lose access to your database!
For more information on Challenge Response, please see Yubico's website. -
When I use KeeChallenge with KeePass2, it creates an extra file. Why do
I have no such file when using KeePassXC?
Our implementation differs from how KeeChallenge handles YubiKeys. KeeChallenge uses the HMAC secret directly to enhance the database. To make this work, they need to store the secret in a side-car file, encrypted with the response of a challenge-response pair that is calculated ahead of time. In KeePassXC, we do not require any knowledge of the HMAC secret. We use the database's master seed (a random byte string that is part of your database) as challenge and then use the response to encrypt the database. That way we do not need an extra file and also gain the advantage that the required response changes every time you save the database, which resembles actual two-factor authentication more closely.
-
When I secure my database in KeePass2 with a YubiKey, I can't open it in
KeePassXC (or vice versa), why?
Due to the fact that our YubiKey implementation differs from KeeChallenge's, they are inherently incompatible (see question above). If you need compatibility between KeePass2 and KeePassXC, you cannot use YubiKeys at the moment.
-
Why only HMAC-SHA1? Why not FIDO-U2F or TOTP?
Both FIDO-U2F and TOTP require a dynamic component (i.e., a counter or timestamp) for successful authentication. This is perfect for authenticating at an online service, but doesn't work for an offline database which needs to be encrypted with a fixed key. HMAC-SHA1, on the other hand, can be computed ahead of time as it only needs a fixed secret and no dynamic component of any kind.
-
But the feature list says KeePassXC supports TOTP. I am confused.
We do support generation of timed one-time passwords (TOTP), but do not (and cannot) support it for securing your KeePassXC database. KeePassXC allows you to store TOTP secrets for online services inside a database and generates the corresponding timed one-time passwords for you. For TOTP, see also the question KeePassXC allows me to store my TOTP secrets. Doesn't this undermine any advantage of two-factor authentication?
-
What happens if I break my YubiKey? Can I create backup keys?
You should always make a copy of the HMAC secret that is stored on the YubiKey and keep it in a secure location. This can be an analog paper copy, but since the YubiKey personalization tool allows you to program a custom secret into the key, you may as well program a second key with the same secret.
-
Can I register multiple YubiKeys with my KeePassXC database?
You can only use a single secret for encrypting the database. So you can use multiple YubiKeys, but they all have to be programmed with the same secret (see question above).
Browser integration
-
Does KeePassXC support browser extensions?
Yes. KeePassXC supports the extension KeePassXC-Browser. You can download it for Mozilla Firefox and Google Chrome / Chromium / Vivaldi. Firefox ESR (52.x) is supported, but the following features are disabled because of WebExtension API limitations:
- Showing context menus on password fields (
menus.ContextType) - HTTP Auth support (
webRequest.onAuthRequired)
- Showing context menus on password fields (
-
How do I connect browser extensions with KeePassXC?
You can enable Browser Integration (KeePassXC-Browser) from the application settings. See the page How to connect KeePassXC-Browser with KeePassXC for more detailed information for the new Browser Integration. For troubleshooting see the following wiki page.
-
How do I fill in additional values on a webpage?
It is possible to fill additional information beyond username, password, and TOTP by defining String Fields on a page.
- From the extension popup menu, click "Choose custom login fields". You can skip the Username, Password, and TOTP fields if not needed.
- On Step 4 (Confirm Selection), choose the additional string fields you need to fill. Note that they are numbered sequentially.
- After choosing the String Fields, go to your KeePassXC client and create advanced attributes with a prefix of 'KPH: ' in the order you chose them above. NOTE: The space after the colon is required.
- If you wish, you may add a short name after the prefix to help you remember its purpose.
An example using the page
https://meine.deutsche-bank.de/trxm/db/init.do:- Choose custom login fields for this page and select Branch, Account and Sub-account as String Fields when you reach step 4.
-
Go to your entry and add the following advanced attributes (the order is critical):
- KPH: Branch
- KPH: Account
- KPH: Sub-account
- Test the filling of the string fields by refreshing the page and using the extension.
SSH Agent integration
-
How does the SSH Agent integration work?
The SSH Agent integration is supported on all target platforms (Linux, macOS and Windows) and it acts as a client for an existing agent. It can automatically add SSH keys from your KeePassXC database to a running SSH agent when unlocked and remove them when locked.
- On Linux, most desktops are already running an agent without any set up required.
- On macOS,
ssh-agentis running by default and no further setup is required. - On Windows, you have multiple options:
- One is to have Pageant running. It is part of the PuTTY suite.
- An alternative is to use e.g. Win32 OpenSSH which may come preinstalled with your Windows 10 version.
- The MSYS2 ssh-agent socket offered by Git for Windows's bundled OpenSSH is not supported
-
What SSH key types are supported?
Most SSHv2 key types are supported (DSA, RSA and Ed25519), including encrypted keys. ECDSA keys are only supported with the new OpenSSH file format. 3DES-encrypted keys are not supported and we highly recommend upgrading them for external storage or store them decrypted inside the database.
- SSHv1 keys are not supported.
- PuTTY format key files (.ppk) are not supported. You can use PuTTY Key Generator (puttygen.exe) to convert your keys to OpenSSH format.
- RFC4716 format key files are not supported.
-
Why are the agent buttons greyed out / why doesn't it work?
On Linux or macOS, you need to have
ssh-agentrunning and theSSH_AUTH_SOCKenvironment variable available for KeePassXC at launch.Arch Linux wiki has a generic guide how to manually run
ssh-agentif it's not already set up. Sometimes other applications like GNOME Keyring orgpg-agentalready provide a compatible agent that also works with KeePassXC.On Windows, either Pageant needs to be running, see How does the SSH Agent integration work? or, alternatively, you need to enable and start the Windows
OpenSSH Authentication Agent(commonly referred to asssh-agent). This process is documented in Microsoft's documentation for user keys.The MSYS2 ssh-agent socket offered by Git for Windows's bundled OpenSSH is not supported.
-
How do I set up a passphrase for encrypted keys?
The SSH Agent integration uses the entry password field as the decryption key.
-
Why does the public key (seem to) have no comment?
When using normal DSA or RSA keys, the private key file does not contain any embedded text. In that case, the entry username field is used as the public key comment. It is also sent to the agent when adding a key and is visible in the agent when listing keys.
If you are using Ed25519 keys or have converted your old key to the new OpenSSH file format, the comment is embedded in the key file which is then used by KeePassXC. You can use
ssh-keygento modify the comment. -
I'm already using KeeAgent, is KeePassXC compatible with it?
Yes, mostly. KeeAgent supports more key types and provides a custom agent, but otherwise you can use the same database with KeeAgent and KeePassXC.
-
Why is Pageant refusing my keys?
Pageant does not support confirm-on-use or automatic removal of key after a timeout. There doesn't seem to be any alternative to Pageant for Windows that supports both of them.
-
Why is OpenSSH ssh-agent refusing my keys?
You may experience an
Agent protocol error
if you are using confirm-on-use option for your keys (e.g. set via the environment variableSSH_ASKPASS_REQUIRE). In that casessh-agentneeds to have assh-askpassprogram available.- On Linux it depends on your distribution and desktop environment how to install and configure one as there are several available.
- On macOS, you need a third party program like theseal/ssh-askpass.
- On Windows the default Windows OpenSSH installation does not support confirm-on-use or automatic removal of key after a timeout.
-
I'm getting protocol or connection errors, what's wrong?
If you are using GNOME Keyring, it is known to be buggy and the SSH Agent implementation fairly incomplete prior to release 3.27.92. You are encouraged to use OpenSSH
ssh-agentif you are stuck with an older version.Known limitations of older versions include no support for Ed25519 keys, no support for confirm-on-use and incorrect implementation of the agent protocol causing protocol errors.
-
I'm getting a "Too many authentication failures" error, what shall I do?
SSH will try all available identity files in sequence when connecting to a server. If you export many SSH keys at a time, you'll very likely experience a "Received disconnect from {port}: Too many authentication failures" error. To solve this issue, you'll have to tell SSH which identity file to use. Either use the
-icommand line option or theIdentityFiledirective in your OpenSSH config file (~/.ssh/config) to pass the path to the respective private key file.If you use the
IdentityFiledirective, you likely want to use theIdentitiesOnlydirective, too. The Arch Linux wiki has a generic guide on how to manage multiple keys.If you prefer storing your private key inside your database using an attachment, you can still do so. Instead of letting the
IdentityFiledirective point to a private key file, let it point to your public key file. The SSH Agent will use the provided information to select the correct private key. -
How do I use KeePassXC SSH Agent integration with Git (Bash) on Windows?
KeePassXC on Windows can be used with Pageant or with Windows OpenSSH.
Git for Windows supports both options since version 2.33.0.You will be prompted during installation of Git for Windows to pick the option you prefer – depending on your Windows version and whether PuTTY is installed.
The MSYS2 ssh-agent socket offered by Git for Windows's bundled OpenSSH is not supported.
If you did not choose Windows OpenSSH during Git installation you can still do the following to make Git (Bash) use Windows OpenSSH: Prepend the path to Windows OpenSSH to the
PATHvariable inside the Git Bash, e.g.export PATH="/c/Windows/System32/OpenSSH:$HOME/bin:$PATH"or use theGIT_SSH_COMMANDenvironment variable (core.sshCommandin the Git configuration file) to override the path to the SSH binary specifically for Git.
Platform-specific
-
Is Auto-Type supported on macOS, Windows and Linux?
Yes, Auto-Type works on all three supported platforms, although on Linux it only works in an X11 session, not Wayland.
-
Does KeePassXC work on mobile phones? If not, which app would you recommend?
We don't have our own mobile app, but you can have the same functionality on both Android and iOS!
- For Android, we recommend KeePassDX and KeePass2Android.
- And for iOS, we suggest Strongbox and KeePassium.
For KeePassXC, porting it properly to mobile platforms would require a full rewrite. You may be able to compile KeePassXC for the mobile OS of your choice, but it isn't at all optimized for mobile screen sizes and form factors, let alone multi-touch input. We also don't see any advantage in providing a mobile version of KeePassXC when there are already excellent options.
-
Why do the tray menu and in-app shortcuts not work on Ubuntu/Unity?
This is a bug caused by
appmenu-qt5. You have 3 options:- Remove the
appmenu-qt5package - Set the environment variable
UBUNTU_MENUPROXY='' - Set the environment variable
QT_QPA_PLATFORMTHEME=''
Note: When you choose the first or third option, KeePassXC will lose the Unity look and feel.
- Remove the
-
I am getting "System Error: VCRUNTIME140_1.dll was not found" when starting KeePassXC. Why?
This error indicates that you are missing the MSVC runtime library (Microsoft Visual C++ Redistributable). You can download the latest version from Microsoft. A download link can also be found on our downloads page.