KeePassXC 2.7.7 released
Posted on in Releases
We’re thrilled to announce the release of KeePassXC version 2.7.7. This update brings several exciting features and enhancements that will improve your workflow and integration with modern authentication services. Let’s dive into the major highlights:
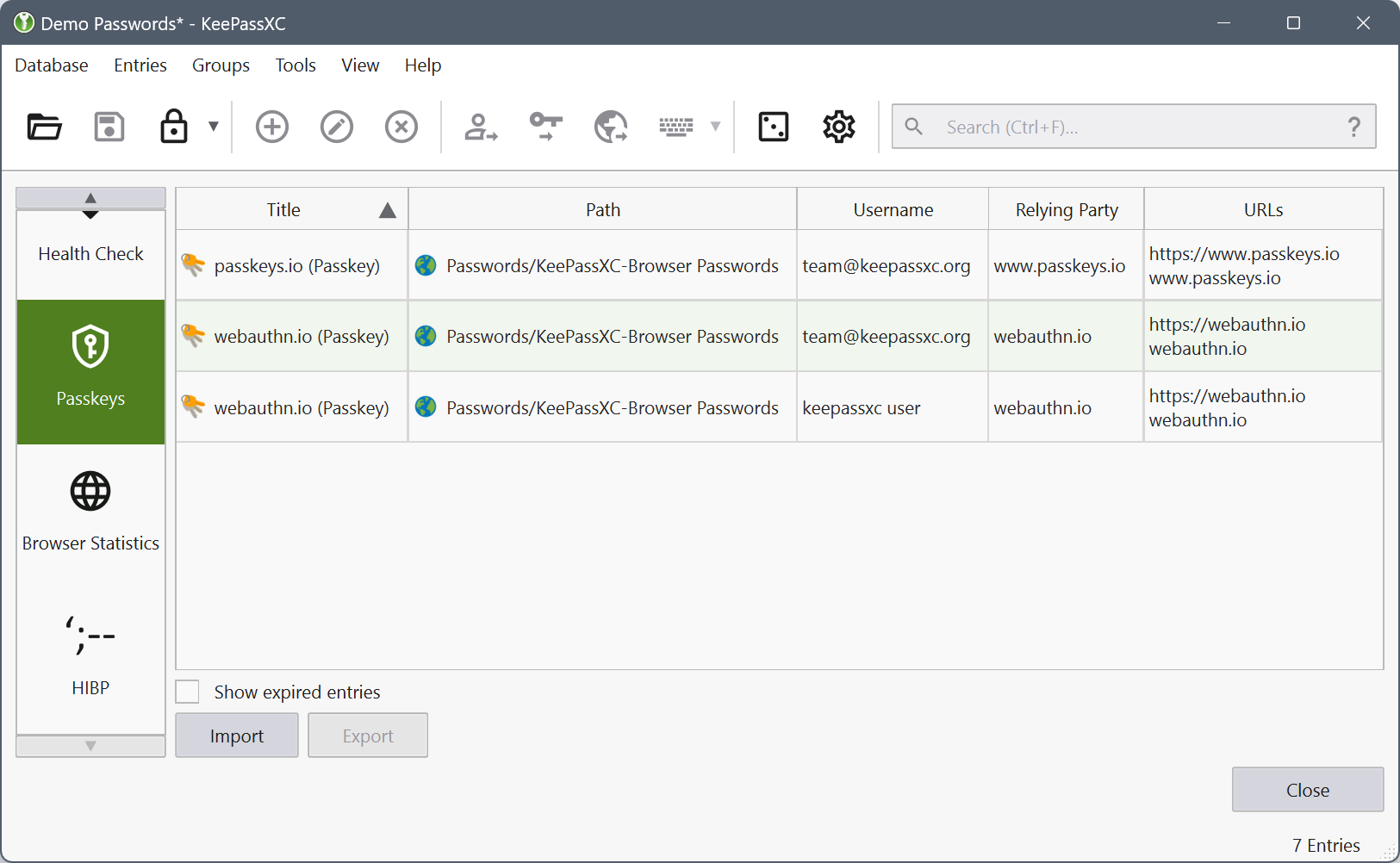
Passkeys Support
This release delivers the official implementation of Passkeys for KeePassXC! This feature is a year in the making and uses the existing browser integration service to both store and use Passkeys for authentication. A special thank you to Ortham for providing an extremely comprehensive standards, security, and privacy review of our implementation prior to release. If you haven’t heard of Passkeys yet, they are an alternative to passwords that are incredibly secure and privacy preserving. Read more about Passkeys and also read our documentation.